So How Legit Is That Wild Car-Hacking Scene in ‘The Fate of the Furious,’ Anyway?
There are a lot of unbelievable things about ‘F8’ — but there could be a kernel of truth to this one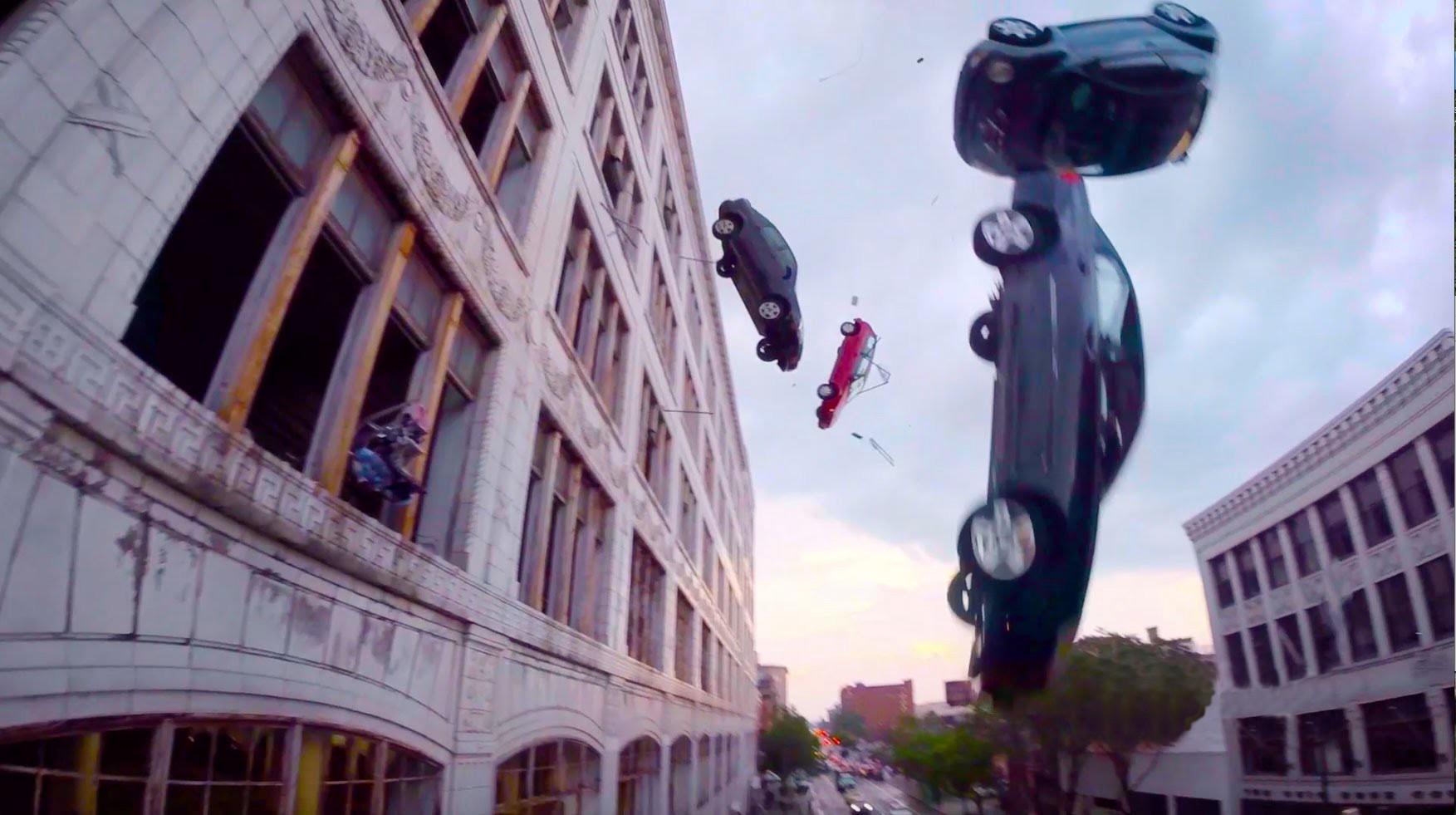
By now you may have been privileged to witness one of the most bombastic scenes in Fast & Furious franchise history, what I have been referring to as "The Revenge of the Camrys." To summarize: International hacker/villain Cipher (Charlize Theron) needs to get a briefcase containing nuclear codes from a foreign minister. For some reason, she decides the best way to do this is by cornering his motorcade as it drives through Times Square. So she instructs a few hacker underlings to type on their keyboards for approximately 30 seconds until they’ve casually commandeered a fleet of zombie cars. The fleet is a potpourri of makes and models, some with terrified drivers still inside. From what seems like a calm and comfortable war room, Cipher’s crew directs them to smash together on the road like a herd of wildebeests, barricading the minister’s escape route. In the hackers’ final push, some cars are even taken over in skyscraper parking garages and ordered to shoot out of openings and onto the minister’s security detail until Cipher finally gets those precious codes.
No part of The Fate of the Furious should be considered even remotely realistic. (Especially the scene where Deckard Shaw seamlessly pairs his smartphone to some wireless Beats headphones so that Dom’s baby can’t hear him kill a bunch of people. Bluetooth still sucks and Beats headphones are not that good at noise cancellation.) Even so, it’s clear this car-hacking scene didn’t come out of nowhere. Action franchises like the Fast & Furious or Bourne movies are in the business of lifting scary headlines from tech news and extrapolating their application to the most horrifying apex. And who can blame them? They’re the only operations with obscene enough budgets to act out our most gruesome collective anxieties about the future.
In this case, the idea to create a zombie army of cars likely originated from a 2015 story by Wired’s Andy Greenberg in which security researchers used something called a zero-day exploit to cut the transmission of his Jeep as he was driving it on the highway. The experiment, executed after months of collaborative research from Charlie Miller (now a security researcher at Chinese ridesharing company Didi Chuxing) and Chris Valasek (Uber’s advanced technologies group security lead), became an instant national story, and struck fear into the hearts of legislators and car owners. As manufacturers had spent the past decade plugging smartphone capabilities into cars, they’d managed to leave a trail of potentially dangerous vulnerabilities behind. If Miller and Valasek could do it, why not Cipher? I emailed Valasek to ask.
"Hahah come on Alyssa," he wrote back in a two-sentence email. "Cars can be hacked but this isn’t a realistic representation … well, of anything, really."
Luckily, Stefan Savage, a University of California–San Diego professor of computer science and engineering, was willing to indulge me in specifics. Savage also has some experience in this field. Back in 2009, he and a team of researchers showed up at General Motors to demonstrate that they could, sight unseen, remotely take control of any of the company’s 2009 models, disable their brakes, and make their engines rev. (GM subsequently spent the next five years working to fix the security flaw.) Savage, too, described the F8 scene as "wildly outside of anything that anyone has ever done," but conceded that a skeleton version of the scenario was possible.
The most salacious vulnerability that Savage and his team exploited was General Motors’ OnStar dashboard operating system. Much like Cipher, Savage was able to use a single computer to take over multiple vehicles. In fact, one version of his team’s attack simply required calling the phone number of an OnStar-equipped car and playing a noise that sounded like a fax machine.
So the most realistic elements of the zombie car scene in question are (1) the fact that Cipher was able to gain access to cars that weren’t necessarily equipped with self-driving software, and (2) that she was able to do it with just a few keystrokes on a computer. But Savage says the major caveat in this scenario is all the legwork that comes before the actual attack.
"There’s some truth to the notion that you can remotely gain access to normal non-Tesla vehicles," he told me. "But it’s not a trivial undertaking. And then on top of that, getting the car to do something you want is even less trivial. Every time it’s specific to the make and model you’re going after … It’s like picking the world’s most complicated lock."
In other words, Cipher and her team of, like, three hackers needed to know which cars they wanted to hijack before causing the world’s most sadistic traffic jam. Or, even less realistically, they would’ve needed to build a comprehensive library of the contact information correlating to every make, model, and year of modern vehicles ever made.
"It’s the kind of thing where if you decided: Alright, this has become a national priority, Manhattan Project–style, we’re going to have the NSA put huge amounts of money and resources into reverse-engineering all of these different cars," Savage said. "And we’re going to somehow need to figure out what their network address, or cellphone [number], or IP address is. If you have huge resources, I can imagine you doing parts of the scenario you described."
In the end, we’re left with two possibilities: Maybe Cipher, amid all her twisted mind games with Dom, is just that good at computers. Or maybe — just maybe — the Fate of the Furious writers didn’t read past a Wired headline. Who can say?